ISO 27001 Information security management is associate in primary example of best apply in data security for any business, no matter its size, and might result in important value savings. The international standard ISO 27001 covers the design, implementation, basic improvement of a information security management system. ISO/IEC specifies the requirements for establishing, implementing, maintaining and continually improving an information security management system within the context of the organization. It also includes requirements for the assessment and treatment of information security risks tailored to the needs of the organization.
- Slide5: Why ISO 27001 Family Standard? While the ISO/IEC 27001 document gives general requirements for an ISMS and is the auditable standard for Information Security Management Systems, there are a family of supporting documents behind it that provide guidelines for planning, implementing, and maintaining an effective ISMS.
- ISO 27001 is meant for certification. ISOhelpline team can provide custom designed ISMS documentation and training programmes specific to your company or inductry segment. Various products for ISO/IEC 27001: 2005 are under development, these products include: 1. PowerPoint Training Slides (PPT) 2. Documentation Manual (Complete Set) 3. Examination system.
- An introduction to ISO 27001 - Information Security Management System Slideshare uses cookies to improve functionality and performance, and to provide you with relevant advertising. If you continue browsing the site, you agree to the use of cookies on this website.
- ISO 27001 has for the moment 11 Domains, 39 Control Objectives and 130+ Controls. Following is a list of the Domains and Control Objectives. Security policy Information security policy.
ISO/IEC 27001 is one of the world's most popular standards and this ISO certification is very sought after, as it demonstrates a company can be trusted with information because it has sufficient controls in place to protect it.
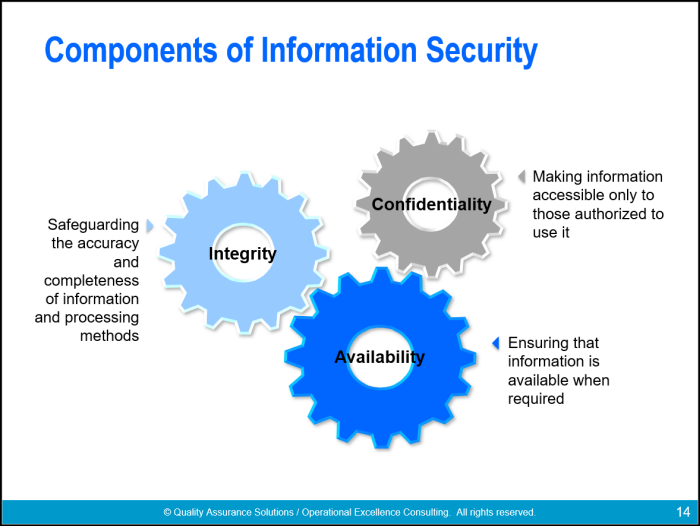
Google, Apple, Adobe, Oracle and many other tech giants, financial institutions, health services providers, insurance companies, education institutions, manufacturing and service companies, large and small business around the world have decided to implement this standard and to get this certification as a proof of their capability to protect the confidentiality, integrity and availability of the information they process.
My course explains the requirements of ISO/IEC 27001 along with the controls in Annex A of this standard to help you understand how an information security management system can be implemented, what are the requirements of this standard and what are the solutions to ensure conformity.
My course is structured into 2 parts:
- the first one is about the management system requirements of ISO/IEC 27001. Context of the organization, leadership, information security policy and objectives, information security risk assessment and treatment, competence and awareness, documented information, operational planning and control, internal audit, management review, nonconformity and corrective action along with all the other requirements of the standard are discussed.
- the second part of the course is all about the controls from Annex A of ISO/IEC 27001 - there are 114 information security controls and all are addressed in the lessons. The topics cover aspects like: Information security policies, organization of information security, mobile devices and teleworking, security of human resources, asset management, classification of information, media handling, access control, user responsibilities, system and application access control, cryptography, physical and environmental security, equipment security, operations security, protection from malware, backup, logging and monitoring, control of operational software, technical vulnerability management, communications security, network security management, information transfer, system acquisition, development and maintenance, security in development and support, supplier relationships, incident management, information security as part of business continuity management, redundancies and compliance.
After going through all the lessons of this course you will have a solid knowledge of what is required for an information security management system, how can an organization implement such a system and get certified to ISO/IEC 27001.
Iso 27001 2013 Standard Pdf
With the information here you can:
- work as a consultant for the implementation of this system in different companies;
Iso 27001 Explained Ppt
- participate in audits (internal or external) on ISO/IEC 27001;
- work in a company that implemented an information security management system or
- if you are manager or owner of a business you will know what is the international standard for information security and start implementing it in your company.
If none of the options above suits your profile you can use the information in my course for awareness on information security and get to know what are the security requirements that so many organizations around the world have decided to adopt.
From my course you will get condensed information that you can re-visit anytime you need and after going through this course Udemy offers the possibility to download a certificate for successful completion so you can demonstrate your competence in the information security field.
Iso 27001 Wikipedia
- Information security managers
- Information security consultants and auditors
- Information security officers
- Information security risk specialists
- Managers and business owners
- People involved in the implementation and administration of information security management systems according to ISO/IEC 27001